From the Open-Publishing Calendar
From the Open-Publishing Newswire
Indybay Feature
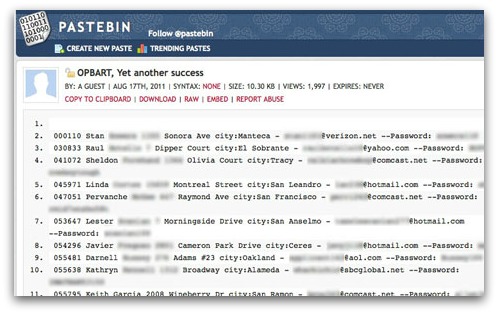
BART officer information hacked and released
Someone has hacked into a database of BART police officers held on bartpoa.com and released names, addresses, emails, and passwords for 102 BART officers.
[User info removed by Indybay editor]
For more information:
http://pastebin.com/XX7DJBqw
Add Your Comments
Comments
(Hide Comments)
notice those cutesy names they use , like ''calsurfr''. he must go surfing on his ''weekends''. thats what they talk about in jails. you are falsely arrested cause of your ''race'', and you have to listen to them talk about their ''beach volleyball'' weekends!! now you see, they see themselves as a comfortable subculture over your maimed body! ''wackichic'' --- wow ,she admits shes awacky and carries a gun for the state!!
i cannot see anyting on pastebin. it says 'unkown paste id'
anyone repost the data somewhere?
anyone repost the data somewhere?
By Lauren Smiley Wed., Aug. 17 2011 at 3:15 PM
[13:42] For starters, this is my first attack on any system.
[13:43] I see. So what called you to action today?
[13:44] What called me to action? Look around you. People trying to stand for themselves in peaceful protest ends up being such a big deal that the police has to shut down cell phone and wifi access.
[13:45] This is exactly like the beginning of the tahrir protests.
[13:46] But let me tell you to important things: I learned how to Inject databases *ONLY* because I wanted to get these passwords and infos.
[13:46] I see. You see this as a better attack that the MyBART one?
[13:46] makes more of a statement?
[13:47] Most important thing is, it was not a hack: They had 0 security.
[13:47] I just exploited a gaping hole.
[13:47] what?
[13:47] A better attack?
[13:48] Listen, don't ask questions.
[13:48] I'll tell you what's important to know first.
[13:48] Ok, go for it.
[13:50] I did it for the lulz.
[13:51] This is a key phrase that any pirate says to the media when it is obvious that they do not care about the movement.
[13:51] Really, this is no big deal.
[13:51] Yet another leak.
[13:51] Yet another cyber attack.
[13:52] You want to sell a dream of cyber attacks like in the movies.
[13:52] Do it without me.
[13:52] Now, let's get to facts about me.
[13:52] I am not american.
[13:52] I am a girl.
[13:53] How was it so easy to get into the site?
[13:53] Care to disclose your nationality?
[13:53] two python scripts of ~50 lines.
[13:54] yeah, sure. How about you give me your adress so I can send you a DNA sample?
[13:55] Was it sql injection on the login fields?
[13:55] <@n0pants> lol
[13:56] No. Here's the security hole: http://bartpoa.com/forms/contact_form.asp?i=0%27%20UNION%20ALL%20SELECT%201,2,3,4,5,%28%27%3C%28%20%27%2buserId%29,%28firstname%2b%27%20%27%2blastname%29,%28address%2b%27%20city:%27%2bcity%29,9,10,11,12,13,14,15,16,%28email%2b%27%20--Password:%20%27%2buserpwd%2b%27%20%29%3E%27%29,18,19,20,21,22,23,24,25,26,27,28,29,30%20FROM%20%2
[13:56] Don't click unlesss you want the feds in your house tomorrow morning.
[13:56] <@n0pants> how did you figure out that query?
[13:57] <@n0pants> just guess the column names?
[13:57] Yes.
[13:57] it took a list of common tables and columns, and a loop.
[13:58] Then, my nice terminal would kindly tell me, quote: "SUCCESS ON userpwd field name."
[13:59] Is the BART POA website still vulnerable right now?
[13:59] Yeah.
[13:59] You have no Idea.
[14:00] Are you planning to grab more from the site?
[14:00] <@n0pants> as a programmer, I'll agree, that's a pretty straightforward attack
[14:00] Somebody more experienced could have gotten the admin password. That would have been way more lulzy.
[14:00] Are you doing this for the lulz or because you think BART overstepped its bounds? You've said both.
[14:01] This is a cyber guerilla is what it is.
[14:02] I got pissed.
[14:02] I learned som stuff.
[14:02] They didn't have protections.
[14:02] I won.
[14:02] As simple as that.
[14:02] You are very dramatic, Lamaline!
[14:02] then again, I had some lulz.
[14:03] How long did it take you to figure out how to get in?
[14:05] A one page PDF tutorial, and this google search: «site:bartpoa.com inurl:.asp?»
[14:05] It took me no time, really.
[14:06] I learned a lot from this attack, though.
[14:06] And I learned a lot about dumping infos.
[14:06] Morality: Use the infos First.
[14:06] then dump.
[14:07] Are you planning to get into get into any other systems?
[14:08] I don't know. I am an opportunist in this matter. But I will never attack unless something is wrong with the actions of the victim.
[14:09] Victim is not the right word: Opponent.
[14:10] You aren't American, but are you in the United States?
[14:10] No.
[14:11] When did you hear about the opBART?
[14:12] I don't remember. I'll be right back.
[14:15] I learned about it 4 days ago.
[14:15] I heard* about it.
[14:16] Ok. I can't resist telling you my nationality.
[14:16] I'm french.
[14:16] Humiliating, huh?
[14:16] <@n0pants> heh
[14:17] and when you say girl, are we talking like teenage?
[14:17] <@n0pants> sfweekly800: see privatemesg (n0pants tab) at some point
[14:18] Not a teenage stricto-sensus.
[14:20] Now, no more private infos.
[14:20] OK.
[14:21] do you know anything about how the mybart.org hack happened?
[14:24] I did not take part in this operation.
[14:24] Lack of information, I guess.
[14:26] are you pleased with your attack?
[14:28] I would say I'm satisfied because it really shows how bad the cyber defense of the enemies of free speech and free movement is. I would say it's promissing.
[14:29] And, that is an encouragement to all those who want to join the cyber guerilla.
[14:32] Is Lamaline always your online handle?
[14:33] No, I made it up for this occasion. I don't know If I'm gonna keep it.
[14:35] All right. Well, thanks for chatting!
[14:35] You're welcome.
[14:35] Thank you.
Follow us on Twitter at @TheSnitchSF and @SFWeekly.
[13:42] For starters, this is my first attack on any system.
[13:43] I see. So what called you to action today?
[13:44] What called me to action? Look around you. People trying to stand for themselves in peaceful protest ends up being such a big deal that the police has to shut down cell phone and wifi access.
[13:45] This is exactly like the beginning of the tahrir protests.
[13:46] But let me tell you to important things: I learned how to Inject databases *ONLY* because I wanted to get these passwords and infos.
[13:46] I see. You see this as a better attack that the MyBART one?
[13:46] makes more of a statement?
[13:47] Most important thing is, it was not a hack: They had 0 security.
[13:47] I just exploited a gaping hole.
[13:47] what?
[13:47] A better attack?
[13:48] Listen, don't ask questions.
[13:48] I'll tell you what's important to know first.
[13:48] Ok, go for it.
[13:50] I did it for the lulz.
[13:51] This is a key phrase that any pirate says to the media when it is obvious that they do not care about the movement.
[13:51] Really, this is no big deal.
[13:51] Yet another leak.
[13:51] Yet another cyber attack.
[13:52] You want to sell a dream of cyber attacks like in the movies.
[13:52] Do it without me.
[13:52] Now, let's get to facts about me.
[13:52] I am not american.
[13:52] I am a girl.
[13:53] How was it so easy to get into the site?
[13:53] Care to disclose your nationality?
[13:53] two python scripts of ~50 lines.
[13:54] yeah, sure. How about you give me your adress so I can send you a DNA sample?
[13:55] Was it sql injection on the login fields?
[13:55] <@n0pants> lol
[13:56] No. Here's the security hole: http://bartpoa.com/forms/contact_form.asp?i=0%27%20UNION%20ALL%20SELECT%201,2,3,4,5,%28%27%3C%28%20%27%2buserId%29,%28firstname%2b%27%20%27%2blastname%29,%28address%2b%27%20city:%27%2bcity%29,9,10,11,12,13,14,15,16,%28email%2b%27%20--Password:%20%27%2buserpwd%2b%27%20%29%3E%27%29,18,19,20,21,22,23,24,25,26,27,28,29,30%20FROM%20%2
[13:56] Don't click unlesss you want the feds in your house tomorrow morning.
[13:56] <@n0pants> how did you figure out that query?
[13:57] <@n0pants> just guess the column names?
[13:57] Yes.
[13:57] it took a list of common tables and columns, and a loop.
[13:58] Then, my nice terminal would kindly tell me, quote: "SUCCESS ON userpwd field name."
[13:59] Is the BART POA website still vulnerable right now?
[13:59] Yeah.
[13:59] You have no Idea.
[14:00] Are you planning to grab more from the site?
[14:00] <@n0pants> as a programmer, I'll agree, that's a pretty straightforward attack
[14:00] Somebody more experienced could have gotten the admin password. That would have been way more lulzy.
[14:00] Are you doing this for the lulz or because you think BART overstepped its bounds? You've said both.
[14:01] This is a cyber guerilla is what it is.
[14:02] I got pissed.
[14:02] I learned som stuff.
[14:02] They didn't have protections.
[14:02] I won.
[14:02] As simple as that.
[14:02] You are very dramatic, Lamaline!
[14:02] then again, I had some lulz.
[14:03] How long did it take you to figure out how to get in?
[14:05] A one page PDF tutorial, and this google search: «site:bartpoa.com inurl:.asp?»
[14:05] It took me no time, really.
[14:06] I learned a lot from this attack, though.
[14:06] And I learned a lot about dumping infos.
[14:06] Morality: Use the infos First.
[14:06] then dump.
[14:07] Are you planning to get into get into any other systems?
[14:08] I don't know. I am an opportunist in this matter. But I will never attack unless something is wrong with the actions of the victim.
[14:09] Victim is not the right word: Opponent.
[14:10] You aren't American, but are you in the United States?
[14:10] No.
[14:11] When did you hear about the opBART?
[14:12] I don't remember. I'll be right back.
[14:15] I learned about it 4 days ago.
[14:15] I heard* about it.
[14:16] Ok. I can't resist telling you my nationality.
[14:16] I'm french.
[14:16] Humiliating, huh?
[14:16] <@n0pants> heh
[14:17] and when you say girl, are we talking like teenage?
[14:17] <@n0pants> sfweekly800: see privatemesg (n0pants tab) at some point
[14:18] Not a teenage stricto-sensus.
[14:20] Now, no more private infos.
[14:20] OK.
[14:21] do you know anything about how the mybart.org hack happened?
[14:24] I did not take part in this operation.
[14:24] Lack of information, I guess.
[14:26] are you pleased with your attack?
[14:28] I would say I'm satisfied because it really shows how bad the cyber defense of the enemies of free speech and free movement is. I would say it's promissing.
[14:29] And, that is an encouragement to all those who want to join the cyber guerilla.
[14:32] Is Lamaline always your online handle?
[14:33] No, I made it up for this occasion. I don't know If I'm gonna keep it.
[14:35] All right. Well, thanks for chatting!
[14:35] You're welcome.
[14:35] Thank you.
Follow us on Twitter at @TheSnitchSF and @SFWeekly.
For more information:
http://blogs.sfweekly.com/thesnitch/2011/0...
We are 100% volunteer and depend on your participation to sustain our efforts!
Get Involved
If you'd like to help with maintaining or developing the website, contact us.
Publish
Publish your stories and upcoming events on Indybay.
Topics
More
Search Indybay's Archives
Advanced Search
►
▼
IMC Network